How Do Websites Track Users With Javascript? | Onlinesim
- Nov 29, 2022, 12:46 PM
- 7 minutes
The website downloads content automatically when you visit YouTube, Netflix, or Google Maps. Pages are always adapted to your device and browser. What happens is that the site has identified your device and used JavaScript to pull in content.
In addition to creating dynamic and interactive web content, JS collects users' information that advertisers and hackers can take advantage of.
The fourth article from cybersecurity series will tell you what JavaScript is and how it is used for tracking.
What Is JavaScript?
JavaScript is a programming language that adds various dynamic content to sites: menus, sounds, and other interactive elements. The language had more simple purposes previously. For instance, Javascript checks if all fields are filled in before submitting.
Today, Javascript is used for creating all kinds of apps, such as interactive maps, 2D and 3D animation, and video players in browsers.
Javascript works like this: a user performs a certain action → a browser identifies it → activates JS-code → a given change is made.
Besides, Javascript can help sites learn about users interacting with the script.
The meta tags contain links to scripts that run after you open a page. A code is triggered when a user visits a site and identifies the user's browser.
Other scripts can start automatically and read information about your screen and activity on the site.
What Can JavaScript Learn About You?
With JavaScript, other codes can be implemented into a site that obtains your browser and PC settings information. JS helps sites to learn the following information about users:
User's interests. It works through a tracking code. This code helps advertisers, webmasters and marketers analyze visitors and their actions on the site. It includes information about how long users read content, which ads they click on, and so on. Then the information goes to Google Analytics, Yandex Metrica, and other analytics systems.
Information about devices. JavaScript code has the navigator code object. It contains the name of the user's operating system and full browser details. If you link a code to the site button, the site will get information about the user after they click the button.
The screen code object holds information about a user's screen. The site owners can know your device's screen size and colors.
The navigator.plugins code objects collect information about plugins and their versions.
Words you type. If this code is already built into the site or hackers have built it in, they can track text fields that users fill in.
This way, for example, hackers can find out bank card details through a phishing payment site.
Camera Information. Special codes can give access to the camera or microphone of your device.
For example, site owners can access your device's microphone and back & front cameras and see what a user is doing.
How does Web Analytics work with JavaScript?
Site owners can also get information such as users' viewed pages, their activity, how users interact with phone numbers given on a site, and how much time they spend on a site.
Some popular services are Google Analytics, Hotjar, Statcounter, and others.
These services show how many people sign in, what items they buy, add to the shopping cart, or just look at, and so on.
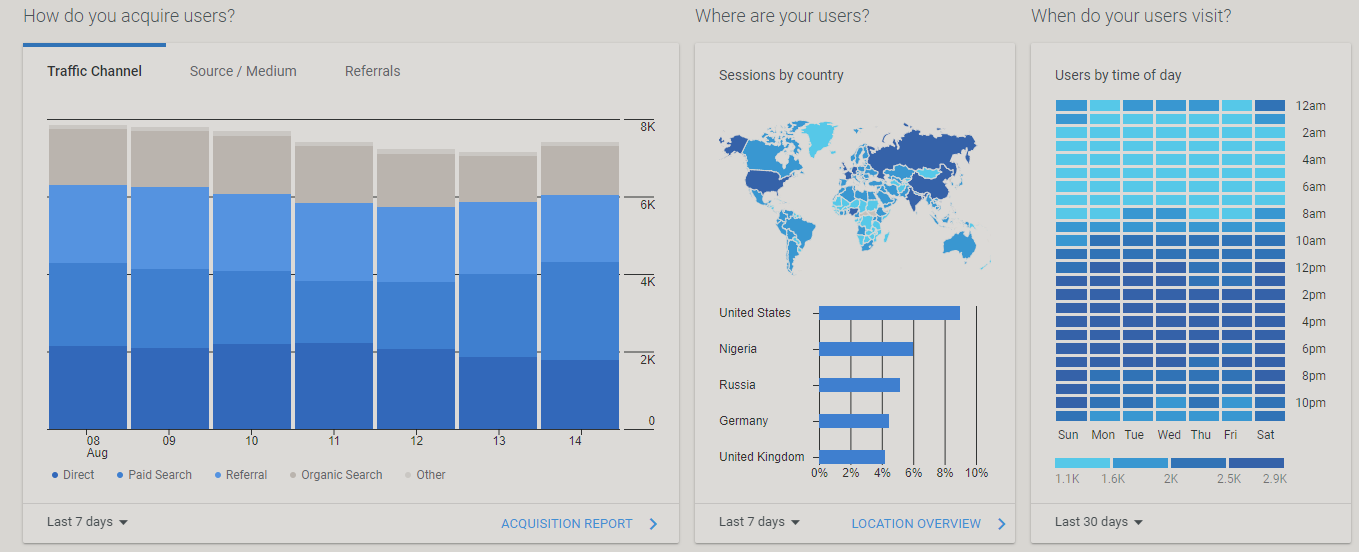
Such analytics systems are installed on almost all sites. They are completely legal and controlled by large companies. Analytics systems monitor only user behavior and do not store personal information. So the site owners cannot link users' online activity with real people. They only get aggregated data. And if they try to obtain users' information and sell it, they will be fined or banned.
The purpose of such systems is to make websites convenient and useful and analyze users' actions on a site.
Why to Disable JavaScript?
When a person visits a site, JavaScript code programs are launched automatically. If malicious code is embedded in JavaScript, users' information may be leaked, or their PC may get viruses.
Thus, disabling JavaScript protects against online spying, as websites will not know which browser or PC you use, what you type, and what internet actions you perform.
What Happens if JavaScript Is Disabled?
If you disable JavaScript, many sites will not work properly. Most sites use JavaScript to interact with the user and display personalized content.
For instance, video hosting sites will not work — the main page will not load. Social networks, online maps, food delivery services, etc., will show empty pages.
If you disable JavaScript, you can also protect yourself from online spying and reduce the chances of data theft. But it does not ensure complete security.
Besides, if one site gets your personal information, it can share it with others. It is impossible with JavaScript because every website has its own codes.
The metrics of website analytics will not work as well. They use JavaScript code and load automatically when the user visits a site.
Ad analytics systems allow sites to optimize ads and improve their efficiency. Simply put, they show ads to the target audience. If you disable JavaScript, the user will see irrelevant and not personalized ads.
Metrics also help identify problems of the website and areas for improvement.
For example, the Hotjar service creates a sitemap showing how a user engages on a specific part of the page. If there is a non-clickable element that users often click on, developers will fix it.
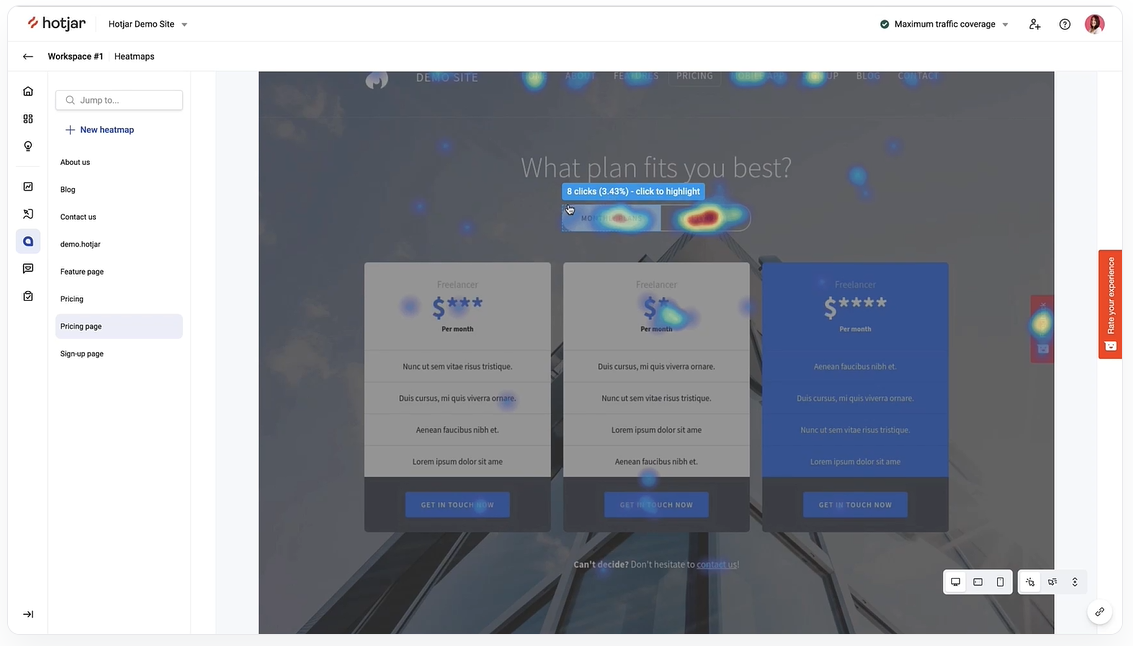
Analytics systems show how visitors interact with a website. The owners of a site will see all user's clicks, cursor movements, the time a person spends on each part of the page, and issues arising in certain browsers or devices.
For instance, if some function does not work in the browser — the site owner will see and fix it.
How Do Hackers Steal Data via JavaScript?
Implementing malicious JS code. It is called cross-site scripting (XSS). This code can process and store users' confidential information.
For example, if a hacker adds a malicious code to an online banking site, they will get login data and other user information.
The hackers changed the script to redirect customer information to a malicious server with a domain name similar to British Airways. The fake server had an SSL certificate, so customers were tricked into believing they were buying tickets on a secure server.
Carrying out SQL injection attack. SQL injection is an injection attack wherein hackers get access to the databases of a site and change or steal user information.
Soon after, other hackers stole 8.3 million emails and passwords from Flaticon users. The attack was also carried out using SQL injection.
Cross-site Request Forgery Attack (CSRF). CSRF is an attack carried out by using a scam website or script. It forces a user to execute unwanted actions on a trusted site to which the user is logged in. The user must click the phishing link for the attack to work.
For example, a person signs in to a banking account and clicks a hacker's link with a request to transfer money to the thief's account. The bank will process the transaction without the user's knowledge because the user is signed in.
How can you protect yourself from data theft via JavaScript?
Visit sites with HTTPS/SSL encryption. Hackers cannot implement malicious JS codes into such a site and will not be able to steal anything. But if a site with HTTPS initially contains malicious JS code — you will not be able to protect yourself.
How to Avoid Tracking via JavaScript?
Use ad blocker extensions to partially avoid surveillance, for example, AdBlock, uBlock Origin, Ghostery, AdGuard, and others.
They block unnecessary scripts and leave those that improve websites and ads.